Modern warfare looks nothing like the industrial-age warfare of World War II. I covered this in The Laptop Luftwaffe, a post I wrote comparing the sabotage of the Iranian nuclear programme ten years ago with the sabotage of the Nazi atom bomb project in the 1940s.
Iran’s nuclear programme isn’t the only cyber-warfare target. The country’s missile programme is also a target.[1] This week President Trump posted a tweet taunting Iran for a missile launch failure.[2] The tweet included a detailed photograph of the damaged launch pad taken from a highly classified Keyhole-11 spy satellite.[3]
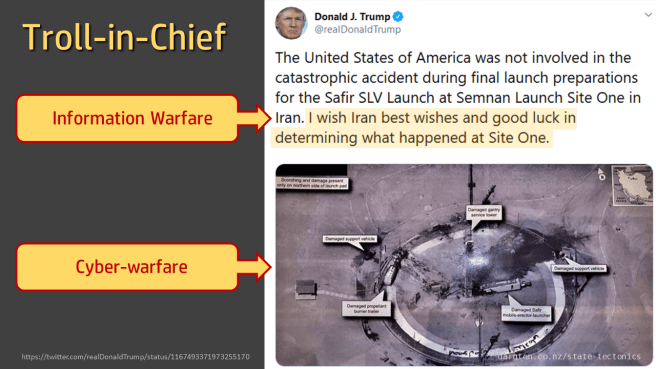
This attack on the Iranian ballistic missile programme invites the same sort of comparisons as the sabotage of the nuclear programme.
The world’s first ballistic missile was Nazi Germany’s A-4/V-2 rocket programme, run from the research station at Peenemünde on Germany’s Baltic coast.

The first V-2 to hit London arrived without warning on the 8th September 1944, killing three people in Chiswick.[4] The second hit a minute later, twenty-five miles away outside Epping. The raids continued for seven months.
There would have a been many more attacks and many more deaths had it not been for a massive raid on the Peenemünde works on the night of the 17th August 1943. The rocket works was considered such an important target that Air Chief Marshall Sir Arthur “Bomber” Harris committed a massive force of nearly six hundred bombers to a dangerous moonlit raid. Forty bombers were lost that night – shot down or crashed – and 245 crew were killed. On the ground, many were killed, including five hundred foreign prisoners working as forced labour.
The raid was judged as success, setting back the Nazi missile programme by months, saving unknown lives in London and, later, in newly liberated parts of France and the Netherlands. The setbacks also ensured that the missiles weren’t ready at the time of the D-Day Normandy landings.
That success came with a heavy loss of life, both in Allied air crew and people on the ground. It’s obvious why the option of a cyber-attack, now that it exists, is preferable.
As I’ve said previously:[5]
The ghostly stealth of a self-replicating software worm could not be more different to the noise, smoke, and violence of an air raid and yet, six decades apart, the results were similar. What used to take an air force is now silent, invisible, and fits in your pocket.
References
[1] https://www.nytimes.com/2019/02/13/us/politics/iran-missile-launch-failures.html
[2] https://twitter.com/realDonaldTrump/status/1167493371973255170
[3] https://sattrackcam.blogspot.com/2019/09/image-from-trump-tweet-identified-as.html
[4] (Middlebrook, 1982)
[5] https://darnton.co.nz/2019/06/09/the-laptop-luftwaffe/
Bibliography
Middlebrook, M. (1982). The Peenemünde Raid. London: Allen Lane.