The age of the self-bombing factory is here. Information age warfare looks as different to an industrial age bombing campaign as telecommuting does to a Chevy Impala.
In 1942, the Allies were desperate to prevent Nazi Germany from developing an atomic bomb. Thirty British Royal Engineers were given the job of sabotaging the heavy water plant in Vemork, in Norway. They were flown from Scotland across the Norwegian Sea in gliders towed behind Halifax bombers. Bad weather and equipment failures meant that both gliders and one of the bombers crashed, killing eleven crew and seven engineers. The remaining 23 engineers were captured, tortured, and shot by the occupying troops.

The second sabotage attempt in February 1943 went better.[1] Five Norwegian saboteurs, trained in Britain, were dropped by parachute onto a remote plateau north of Vemork, where they met up with Norwegian resistance fighters. The team climbed down a steep gorge, crossed a frozen river, and scaled cliffs protecting the heavy water plant. They crawled into the plant through a cable duct, set explosives to destroy the plant, and then escaped into the mountains to begin a multi-week trek to safety in Sweden. The plant was put out of action but rebuilt within six months.
In November the US Air Force assembled a force of 140 B-17 bombers to destroy the plant. They dropped 700 bombs on the town of Vemork, destroying a fertiliser plant and killing 21 civilians, but leaving the crucial heavy water room undamaged.

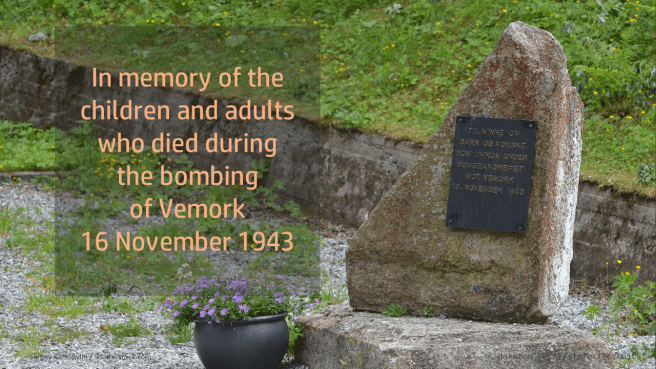
A final attempt to disrupt the programme was made with the sabotage of a ferry carrying railcars full of heavy water. The D/F Hydro was sunk with its cargo, at a cost of 14 civilian lives.
Sixty years later, the United States and Israel were desperate to prevent Iran from developing an atomic bomb. This time there was no air force, no bombing campaign, and nobody was killed. The weapon used to sabotage Iran’s uranium enrichment facility at Natanz was delivered on a USB stick.
In June 2009 a sophisticated software package, later named Stuxnet, was released with the aim of finding its way to Natanz. The Natanz plant housed nearly ten thousand uranium centrifuges, whose job was to separate the bulk of relatively inert uranium-238 from the small fraction of lighter, weapons-grade uranium-235. The centrifuges were precision machines that spun at supersonic speeds, managed by computerised industrial control systems.[2]

The software was designed to hide itself on USB memory sticks so that it could infect computers that were physically separated from the Internet. It had a very specific set of rules, looking for computers that were connected to the exact model of Siemens programmable logic controller known to be running the centrifuges. When it found its target, it would replace the software on the controller with a modified version that would intermittently cause the centrifuges to fail, all the time reporting normal operation.

The machinery had turned on itself and was slowly tearing itself apart. For months, the technicians at Natanz struggled to keep the plant operational but didn’t even know they were under attack.
Around two thousand centrifuges are estimated to have been taken out of service. Doubts about the machines meant the plant never reached full production, setting the Iranian nuclear programme back by years.
The ghostly stealth of a self-replicating software worm could not be more different to the noise, smoke, and violence of an air raid and yet, six decades apart, the results were similar. What used to take an air force is now silent, invisible, and fits in your pocket.
References
[1] (Bascomb, 2016). Ch18
[2] (Zetter, 2014)
Bibliography
Bascomb, N. (2016). The Winter Fortress. London: Head of Zeus.
Zetter, K. (2014). Countdown to Zero Day. New York: Broadway Books.