Series: BTC# – Learning to Program Bitcoin in C#
« Previous: BTC#: Elliptic Curves over Finite Fields
Next: BTC#: Digital Signatures »
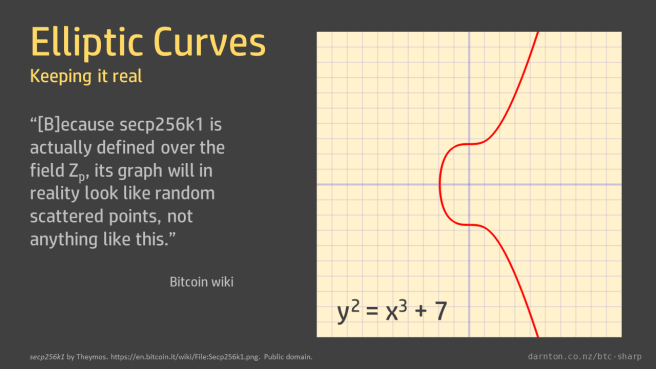
The trick to breaking elliptic curve cryptography is reversing scalar multiplication of points on the curve. When we’ve got curves defined over small finite fields it’s easy: just work out the complete set of multiples (the members of the finite cyclic group) and look up the answer.
That’s why the prime used to define the finite field, and therefore the number of elements in the group, is mindbogglingly big.
The parameters of the secp256k1 curve used by Bitcoin are on the Bitoin Wiki.
I’ve copied those into a static Secp256k1 class. (There is a post on big integers in C# to jog your memory.)
public static class Secp256k1
{
// Highest order bit parsed as sign, so lead with 00.
public static BigInteger P { get; } = BigInteger.Parse("00FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFEFFFFFC2F", NumberStyles.AllowHexSpecifier);
public static BigInteger A = BigInteger.Zero;
public static BigInteger B = new BigInteger(7);
public static BigInteger Gx { get; } = BigInteger.Parse("0079BE667EF9DCBBAC55A06295CE870B07029BFCDB2DCE28D959F2815B16F81798", NumberStyles.AllowHexSpecifier);
public static BigInteger Gy { get; } = BigInteger.Parse("00483ADA7726A3C4655DA4FBFC0E1108A8FD17B448A68554199C47D08FFB10D4B8", NumberStyles.AllowHexSpecifier);
public static BigInteger N { get; } = BigInteger.Parse("00FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFEBAAEDCE6AF48A03BBFD25E8CD0364141", NumberStyles.AllowHexSpecifier);
}
I’ve also added a couple of extra constants to that class. These use the coefficients A and B and the prime P to create a curve object and the generator point coordinates Gx and Gy to create a generator point object.
public static EllipticCurveOverFiniteField Curve { get; } = new EllipticCurveOverFiniteField(A, B, P);
public static EllipticCurveFiniteFieldPoint G = Curve.GetPoint(Gx, Gy);
A couple of unit tests make sure that everything is defined properly.
[TestMethod]
public void Curve_GeneratorPointIsOnCurve()
{
Assert.IsTrue(Secp256k1.Curve.PointIsOnCurve(Secp256k1.Gx, Secp256k1.Gy));
}
[TestMethod]
public void GeneratorPointHasOrderN()
{
Assert.IsTrue((Secp256k1.N * Secp256k1.G).AtInfinity);
}
Note that the multiplication N x G, which checks the order of the generator point, would take vastly longer than the age of the universe to calculate by repeated addition but takes milliseconds when done by binary expansion.
This approach is slightly different to the one taken in the book, so compare them and use whichever you prefer.
« Previous: BTC#: Elliptic Curves over Finite Fields
Next: BTC#: Digital Signatures »